Another day, another ransomware: NotPetya
- Details
- Category: Social Engineering
- Published: Wednesday, 28 June 2017 15:34
Written by Federico Valentini, CEFRIEL
Another day, another ransomware.
This new strain is called Petya, or Petrwap, or NotPetya and according with multiple sources, Ukraine is the most targeted country followed by Russia. What we saw in the early hours of propagation were so many technical analyses, many of which turned out to be wrong or inaccurate.
At the time of writing, I can say that this is not the usual ransomware campaign we are used to see because right now it’s clearer that NotPetya is definitely not designed to make money, but rather to cause damage, spreading fast and globally, camouflaging to look like the original Petya ransomware.

Figure 1 - Percentage of infection by country
Few elements in support of this thought:
- Single hardcoded BTC address for paying the ransom for each victim, while most ransomware strains create a custom BTC address for each victim. At this moment, the attacker(s) collected barely 44 transactions and while I was analysing them, one specific transaction caught my attention, as you can see in Figure 2.

Figure 2 - A specific (and hilarious) transaction to the attacker(s) wallet
- “Payment & Restore” process required to send an email including the sender bitcoin address among a “personal key installation key” (which is very complex strings for a common user, as shown in Figure 3) to an address that had been immediately disabled by the service provider. This countermeasure makes the recovery mechanism unusable and probably the attacker(s) was already aware of it.
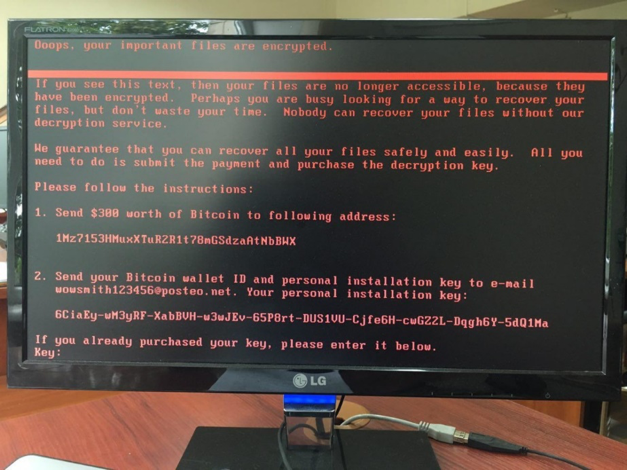
Figure 3 - NotPetya screen
Furthermore, there are main differences between NotPetya and the last global ransomware called WannaCry which was spread entirely using SMBv1 (ETERNALBLUE) and all the infected systems began to scan and, in their turn, infect other systems. This causes a global and exponential infection. NotPetya, instead, is spreading itself only inside local network and not over the entire Internet, so the probability of being victim of the attack is lower because it requires that the system is already on the same subnet of another infected device.

Figure 4 - Infection methods of NotPetya. Credits: Kryptoslogic
Another difference is related to how the initial dropper was spread: in WannaCry it seems to have been spread by an infected document, while in NotPetya the dropper was spread through a fake MeDoc update, a software widely used by Ukrainian companies for paying taxes. That’s why Ukraine was the most hit country in this malware campaign. Furthermore, every company that does business in Ukraine (and obviously pay taxes there) with high probability use MeDoc and that’s why this attack hit also many other foreign companies.
There are also claims about using of spear-phishing campaigns to expand the infection globally but, at the time of writing, this information is not yet confirmed.
Malware Tech Blog (@MalwareTechBlog) provides another plausible (but not confirmed) theory[1] about how the ransomware was deployed widespread without using spear-phishing campaign: it could be possible thanks to ETERNALBLUE exploit and network misconfiguration.

Figure 5 - Certificate issue of the fake update
Despite the technical aspects of the propagation, a relevant role in the attack is also played by social engineering. Indeed, we can highlight three main aspect related to Social Engineering techniques used by the attacker(s), summarized in the following points:
- The initial compromise of MeDoc servers was most likely (even if not yet confirmed) performed thought a spear-phishing campaign against selected MeDoc employees.
- The mechanism used to spread the attack through the fake update, could have been easily detected by users, since it did not have a valid digital signature (as shown in Figure 5), but probably due to lack of user awareness, this mechanism results actually effective.
- NotPetya, during the infection, drops a credential dumping tool (i.e. Mimikatz) and use the captured credentials to run itself in remote computers using either PSEXEC or WMIC. Through this technique, attacker(s) relies on typical user’s bad habits of sharing administration credentials on different devices: this fact enables the possibility to deliver the malware on every machine, despite they were either fully pathed or not.
In conclusion, this is another relevant attack and, again, Social Engineering in general (meant as the overall sum of the techniques adopted to involve humans and assign them a crucial role in the attack spreading), played a significant role in this widespread infection. Security experts still warning about NotPetya and other ransomwares that will continue to proliferate as long as companies delay patching process and fail a robust response plan. Furthermore, most companies ignore what is the weakest link of the security-chain: the human factor. As a consequence, companies became tremendously exposed to the newest Social Engineering techniques and thus prone to targeted cyber-attacks.
The DOGANA project focuses on the impact and the remediation of the human factor in security, which is one of the most demanding challenges of today’s security and for which no widely accepted and stable solutions currently exist.
[1] https://www.malwaretech.com/2017/06/petya-ransomware-attack-whats-known.html
Sources:
https://krebsonsecurity.com/2017/06/petya-ransomware-outbreak-goes-global/
https://www.theregister.co.uk/2017/06/28/petya_notpetya_ransomware/
https://medium.com/@thegrugq/pnyetya-yet-another-ransomware-outbreak-59afd1ee89d4
https://gist.github.com/vulnersCom/65fe44d27d29d7a5de4c176baba45759
https://www.malwaretech.com/2017/06/petya-ransomware-attack-whats-known.html
by Federico Valentini (CEFRIEL)





